top command
We’ve already learned that Splunk’s search language is called Search Processing Language (SPL). This language contains hundreds of search commands and their functions, arguments and clauses. In this section we will describe the top command, which can be used to display the most common values of a field, along with their count and percentage.
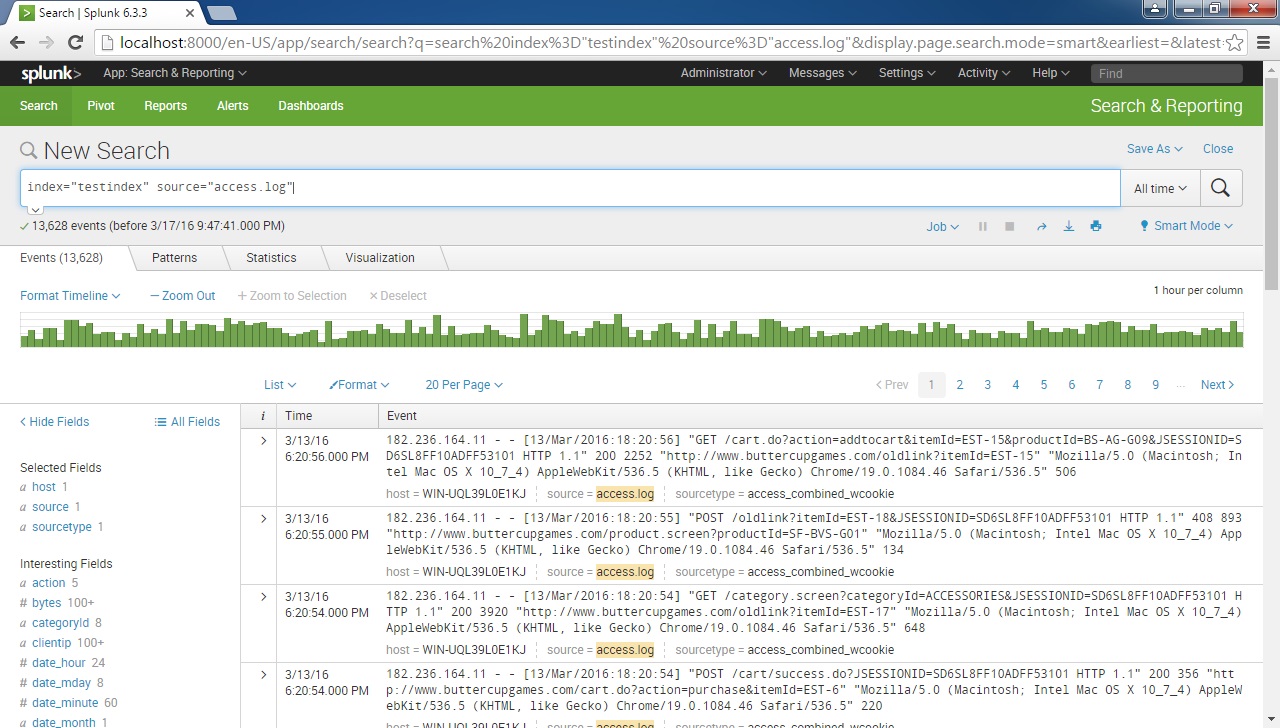
Consider the following example search:
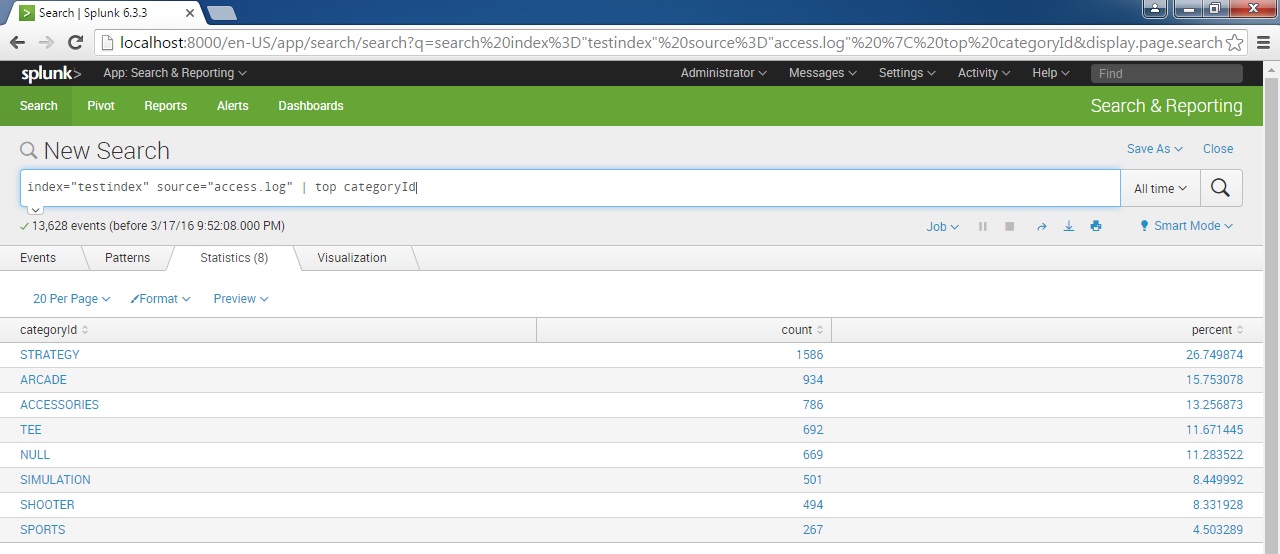
As you can see on the left, Splunk has extracted fields from event data. If we want to display the top categories using the top command with the categoryId field:
As you can see from the output above, the top command has displayed the names of the most common categories of the events, along with their count and percentage