Port security feature
All interfaces on a Cisco switch are turned on by default. This means that an attacker could connect his laptop to your network through a wall socket and potentially perform an attack on your network. Luckily, there is a feature on Cisco switches called port security that can help you mitigate the threat.
With port security, you can associate specific MAC addresses with specific interfaces on your switch. This enables you to restrict access to an interface so that only the authorized devices can use it. If an unathorized device is connected, you can decidethe action that the switch will take, such as discarding the traffic, sending an alert, or shutting down the port.
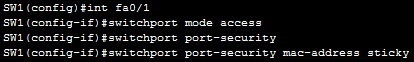
Three steps are required to configure port security:
- defining the interface as an access interface using the switchport mode access interface subcommand.
- enabling port security using the switchport port-security interface subcommand.
- defining which MAC addresses are allowed to send frames through this interface using the switchport port-security mac-address MAC_ADDRESS interface subcommand or using the switchport port-security mac-address sticky interface subcommand. The sticky keyword instruct the switch to dynamically learn the MAC address of the currently connected host.
Two steps are optional:
- defining the action that the switch will take when a frame from an unathorized device is received. This is done using the port security violation {protect | restrict | shutdown}
interface subcommand. All three options discard the traffic from the unauthorized device. The restrict and shutdown options send a log messsages when a violation occurs. Shutdown mode also shuts down the port. - defining the maximum number of MAC addresses that can be received on the port using the switchport port-security maximum NUMBER interface submode command
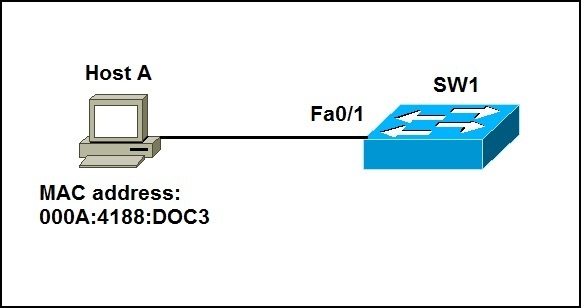
Here is a simple example:
Host A is connected to Fa0/1 on SW1. To enable port security on Fa0/1, we need to define the port as an access port, enable port security and define which MAC addresses are allowed to send frames through this interface. We can do this with the following set of commands:
Using the show port-security interface fa0/1 command on SW1, we can see that the switch has learned the MAC address of Host A:
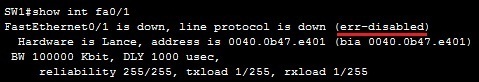
By default, the maximum number of allowed MAC addresses is one. Consider what happens if we connect a different host to the same port:
By default, if a security violation occurs, the switch will shut down the offending port. In the picture above, you can see the status code of err-disabled on Fa0/1, which means that the security violation has occured on the port.