The reason flag
By default, an Nmap output indicates whether a host is up or not, but does not describe the discovery tests that the host responded to. It can be useful to understand the reason why a port is marked as open, closed, or filtered and why the host is marked as alive. This can be done using the --reason flag. Here is an example:
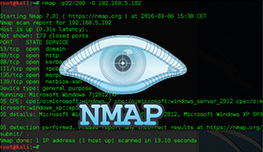
root@kali:~# nmap -T4 --reason 192.168.5.102 Starting Nmap 7.01 ( https://nmap.org ) at 2016-03-05 18:36 CET Nmap scan report for 192.168.5.102 Host is up, received reset ttl 128 (1.0s latency). Not shown: 977 closed ports Reason: 977 resets PORT STATE SERVICE REASON 21/tcp open ftp syn-ack ttl 128 53/tcp open domain syn-ack ttl 128 80/tcp open http syn-ack ttl 128 88/tcp open kerberos-sec syn-ack ttl 128 111/tcp open rpcbind syn-ack ttl 128 135/tcp open msrpc syn-ack ttl 128 139/tcp open netbios-ssn syn-ack ttl 128 389/tcp open ldap syn-ack ttl 128 445/tcp open microsoft-ds syn-ack ttl 128 464/tcp open kpasswd5 syn-ack ttl 128 514/tcp filtered shell no-response 593/tcp open http-rpc-epmap syn-ack ttl 128 636/tcp open ldapssl syn-ack ttl 128 2049/tcp open nfs syn-ack ttl 128 3260/tcp open iscsi syn-ack ttl 128 3268/tcp open globalcatLDAP syn-ack ttl 128 3269/tcp open globalcatLDAPssl syn-ack ttl 128 49152/tcp open unknown syn-ack ttl 128 49153/tcp open unknown syn-ack ttl 128 49154/tcp open unknown syn-ack ttl 128 49155/tcp open unknown syn-ack ttl 128 49157/tcp open unknown syn-ack ttl 128 49158/tcp open unknown syn-ack ttl 128 Nmap done: 1 IP address (1 host up) scanned in 65.63 seconds
In the output above you can see that Nmap has included the packet type that determined the port and host state. For example, the port 21 was marked as open because the SYN-ACK packet was received, which means that a service on that port attempted to complete the TCP three-way handshake.