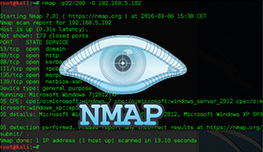
Packet trace
Nmap allows you to trace the packets it is sending, so you can view all sent and received packets. If you ever worked with tcpdump, a Linux-based packet sniffer, you will be familiar with the Nmap output. To enable packet tracing, use the --packet-trace flag. Here is an example:
root@kali:~# nmap -sn --packet-trace 192.168.5.102 Starting Nmap 7.01 ( https://nmap.org ) at 2016-03-04 21:37 CET SENT (0.0037s) ICMP [192.168.198.149 > 192.168.5.102 Echo request (type=8/code=0) id=63393 seq=0] IP [ttl=40 id=8339 iplen=28 ] SENT (0.0044s) TCP 192.168.198.149:47215 > 192.168.5.102:443 S ttl=39 id=64060 iplen=44 seq=1954198708 win=1024 <mss 1460> SENT (0.0051s) TCP 192.168.198.149:47215 > 192.168.5.102:80 A ttl=54 id=59660 iplen=40 seq=0 win=1024 SENT (0.0059s) ICMP [192.168.198.149 > 192.168.5.102 Timestamp request (type=13/code=0) id=33500 seq=0 orig=0 recv=0 trans=0] IP [ttl=54 id=15717 iplen=40 ] RCVD (0.0050s) TCP 192.168.5.102:80 > 192.168.198.149:47215 R ttl=128 id=14236 iplen=40 seq=1954198708 win=32767 NSOCK INFO [0.0060s] nsock_iod_new2(): nsock_iod_new (IOD #1) NSOCK INFO [0.0060s] nsock_connect_udp(): UDP connection requested to 192.168.198.2:53 (IOD #1) EID 8 NSOCK INFO [0.0060s] nsock_read(): Read request from IOD #1 [192.168.198.2:53] (timeout: -1ms) EID 18 NSOCK INFO [0.0060s] nsock_write(): Write request for 44 bytes to IOD #1 EID 27 [192.168.198.2:53] NSOCK INFO [0.0060s] nsock_trace_handler_callback(): Callback: CONNECT SUCCESS for EID 8 [192.168.198.2:53] NSOCK INFO [0.0060s] nsock_trace_handler_callback(): Callback: WRITE SUCCESS for EID 27 [192.168.198.2:53] NSOCK INFO [0.0100s] nsock_trace_handler_callback(): Callback: READ SUCCESS for EID 18 [192.168.198.2:53] (44 bytes): O<...........102.5.168.192.in-addr.arpa..... NSOCK INFO [0.0110s] nsock_read(): Read request from IOD #1 [192.168.198.2:53] (timeout: -1ms) EID 34 NSOCK INFO [0.0110s] nsock_iod_delete(): nsock_iod_delete (IOD #1) NSOCK INFO [0.0110s] nevent_delete(): nevent_delete on event #34 (type READ) Nmap scan report for 192.168.5.102 Host is up (0.00013s latency). Nmap done: 1 IP address (1 host up) scanned in 0.01 seconds
In the output above you can see useful info about send and received packets, such as source and destination IP addresses, TTL, sequence number, etc.