Specify port ranges
By default, Nmap scans the most common 1,000 ports for each protocol. However, there are 65535 ports that can be used for service, and sometimes you will want to scan very high ports or even individual ports. To do this, the -p flag is used.
Here are a couple of examples. To scan only the port 22, we can use the following command:
root@kali:~# nmap -p 22 192.168.5.102
Starting Nmap 7.01 ( https://nmap.org ) at 2016-03-04 16:23 CET
Nmap scan report for 192.168.5.102
Host is up (0.00034s latency).
PORT STATE SERVICE
22/tcp filtered ssh
Nmap done: 1 IP address (1 host up) scanned in 0.23 seconds
To scan a range of ports, use the hyphen to specify the range. For example, to scan ports 50 to 60, we can use the following command:
root@kali:~# nmap -p 50-60 192.168.5.102
Starting Nmap 7.01 ( https://nmap.org ) at 2016-03-04 16:24 CET
Nmap scan report for 192.168.5.102
Host is up (0.74s latency).
PORT STATE SERVICE
50/tcp closed re-mail-ck
51/tcp closed la-maint
52/tcp closed xns-time
53/tcp open domain
54/tcp closed xns-ch
55/tcp closed isi-gl
56/tcp closed xns-auth
57/tcp closed priv-term
58/tcp closed xns-mail
59/tcp closed priv-file
60/tcp closed unknown
Nmap done: 1 IP address (1 host up) scanned in 1.04 seconds
To exclude certain ports from scanning, use the --exclude-ports flag. For example, to exclude ports 1 to 100 from scanning, we would use the following command:
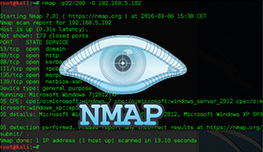
root@kali:~# nmap --exclude-ports 1-100 192.168.5.102
Starting Nmap 7.01 ( https://nmap.org ) at 2016-03-04 16:26 CET
Nmap scan report for 192.168.5.102
Host is up (1.0s latency).
Not shown: 981 closed ports
PORT STATE SERVICE
111/tcp open rpcbind
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
514/tcp filtered shell
593/tcp open http-rpc-epmap
636/tcp open ldapssl
2049/tcp open nfs
3260/tcp open iscsi
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49157/tcp open unknown
49158/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 103.70 seconds
It is also possible to scan fewer ports than the default 1000. With the -F flag, you can reduce the number of scanned ports to 100.